The web is filled with malicious pages. Sadly, these also can seem on the websites of your prospects/suppliers.
No firm at present has an integration that originates from or gives enter to a buyer or provider’s web site. After all, your online business can’t exist with out these providers, however typically it’s a menace due to these providers. The exterior websites you work together with could include malicious content material (whether or not put in on function or compromised by a 3rd celebration), and if that content material finds its solution to the predetermined place, the implications might be disastrous.

Cannot we manually scan web sites for malicious pages?
It might appear {that a} competent developer ought to be capable of scan pages for vulnerabilities. Sadly, this isn’t even near actuality for a lot of causes:
- Builders will not be specialised in detection/safety. Their experience lies in constructing complicated software program by assembling a lot smaller subsystems; in different phrases, they merely do not have the abilities.
- Even should you got here throughout a proficient sufficient developer, the duty would merely be an excessive amount of. A typical feature-rich internet web page comprises hundreds of strains of code; pasting all of them collectively to work out the larger image, in addition to the little loopholes, is nothing in need of a nightmare. You may as nicely order somebody to eat an entire elephant for lunch!
- To cut back web page load instances, web sites usually compress and minify their CSS and JavaScript information. This leads to such a large number of code that it’s utterly not possible to learn.
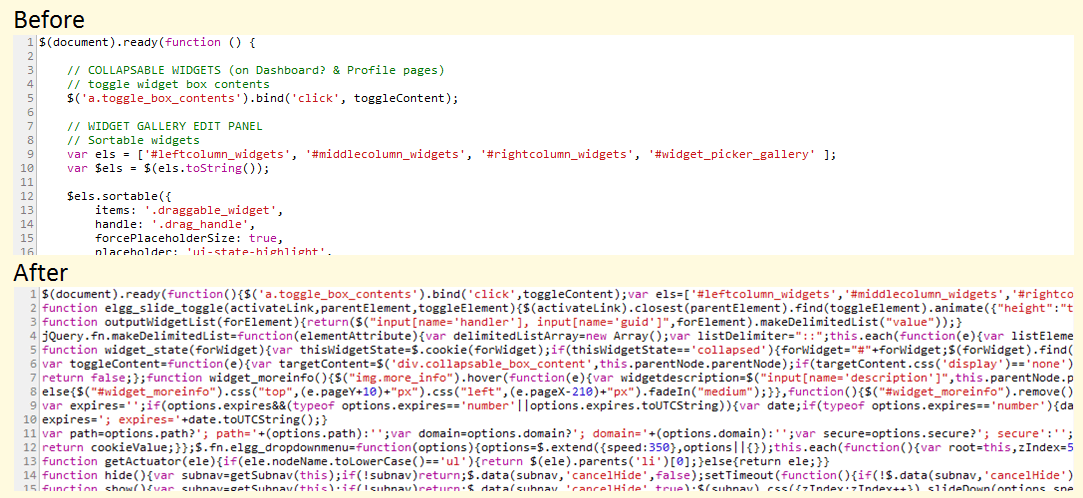
If this nonetheless seems to be readable, it is as a result of the nice souls there determined to maintain the variable names inside a giant context. Attempt the supply code for jQuery, which somebody can host on their web site and tamper with (two strains down someplace on this mess):
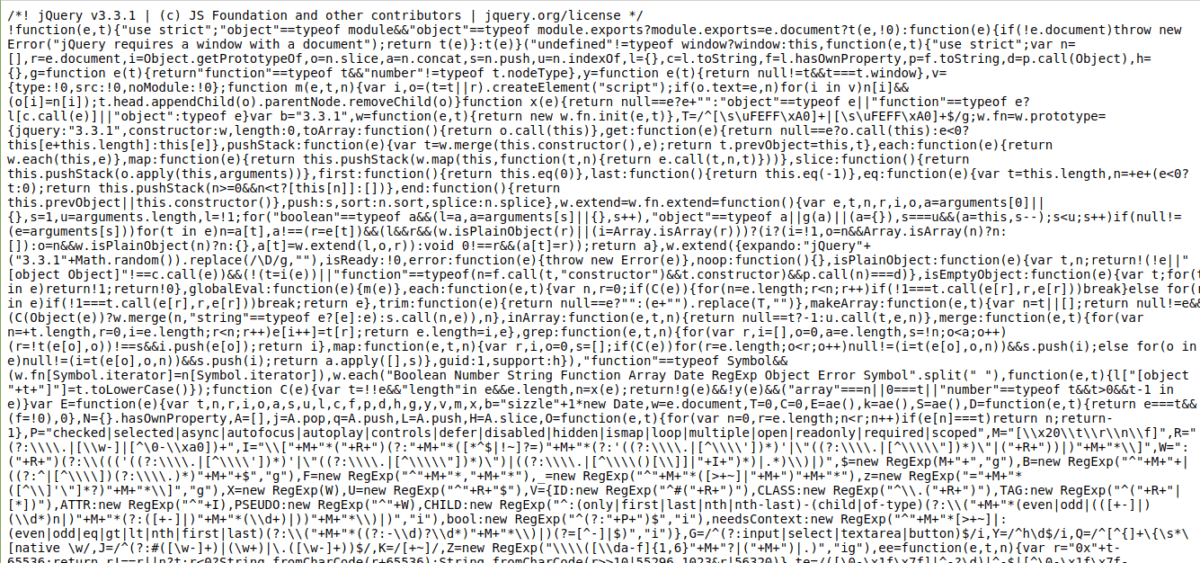
To not point out that the supply comprises nearly 5,000 strains of code. 😎
This is only one script we’re speaking about. An internet web page usually has 5 to fifteen scripts related to it, and it’s possible that you can be working with 10 to twenty internet pages in whole. Think about having to do that each day. . . Or worse, a couple of instances a day!
Thankfully, it’s attainable to scan URLs rapidly and simply by way of APIs. You can’t solely scan internet pages, but in addition information which are provided to you for obtain. Let’s check out some API instruments that will help you do that. And oh, since these are APIs, your developer’s efforts can be a lot better served should you ask them to construct a web site scanner instrument utilizing these APIs. 😀
Google Net danger
It is no shock that an internet web page audit comes from the corporate that virtually owns the web (all internet pages, I imply). However there is a catch: Google Net Threat continues to be in beta and is simply obtainable on demand. Being in beta means extra drastic adjustments.
However because the API is kind of easy, any adjustments could be addressed by your developer with the assistance of an API monitoring instrument and some minutes of growth time. 🙂
Utilizing the API can also be tremendous simple. To verify a single web page by way of the command line, merely ship a request like this:
curl -H "Content material-Sort: utility/json" "https://webrisk.googleapis.com/v1beta1/uris:search?key=YOUR_API_KEY&threatTypes=MALWARE&uri=httppercent3Apercent2Fpercent2Ftestsafebrowsing.appspot.compercent2Fspercent2Fmalware.html"If the request was profitable, the API replies again with the kind of vulnerability on the web page:
{
"menace": {
"threatTypes": [
"MALWARE"
],
"expireTime": "2019-07-17T15:01:23.045123456Z"
}
}As you possibly can see, the API confirms that the web page is thought to include malware.
Please notice that the Google Net Threat API doesn’t carry out on-demand diagnostics on a URL or file of your alternative. It consults a blacklist maintained by Google based mostly on the search outcomes and experiences and experiences whether or not the URL is on that blacklist or not. In different phrases, if this API says a URL is secure, you possibly can safely assume it is fairly secure, however there aren’t any ensures.
VirusTotal
VirusTotal is one other cool service that you should use to scan not solely URLs, but in addition particular person information (in that sense, I rank it above Google Net Threat when it comes to usability). If you happen to really feel like attempting out the service, simply head over to the web site and proper on the homepage there may be an choice to get began.
Whereas VirusTotal is offered as a free platform constructed and maintained by a vibrant group, it does provide a industrial model of its API. Here is why you wish to pay for the premium service:
- Versatile request fee and every day quota (versus the one 4 requests per minute for the general public API)
- The submitted useful resource is scanned by VirusTotal via their antivirus and extra diagnostic info is returned.
- Behavioral details about information you submit (the information are positioned in numerous sandbox environments to observe suspicious exercise)
- Search the VirusTotal file database for numerous parameters (complicated searches are supported)
- Strict SLA and response instances (information submitted to VirusTotal by way of the general public API are queued and take important time for evaluation)
Selecting the proprietary VirusTotal API might be top-of-the-line investments you have ever made in a SaaS product on your enterprise.
Scan
One other suggestion for safety scanner APIs is Scanii. It’s a easy REST API that may scan submitted paperwork/information for the presence of threats. Consider it as an on-demand virus scanner that may run and scale effortlessly!
These are the goodies that Scanii presents:
- Able to detecting malware, phishing scripts, spam content material, NSFW (Not Secure For Work) content material, and so forth.
- It is constructed on Amazon S3 for simple scalability and risk-free file storage.
- Detect offensive, unsafe or probably harmful textual content in over 23 languages.
- A easy, no-nonsense, centered method to API-based file scanning (in different phrases, no unnecessarily “helpful” options)
The nice factor is that Scanii is a meta engine; that’s, it doesn’t carry out scans itself, however makes use of a sequence of underlying engines that do the preliminary work. It is an awesome asset since you’re not tied to any explicit safety engine, which implies you do not have to fret about damaged API adjustments and the like.
I see Scanii as an enormous boon for platforms that depend on user-generated content material. One other use case is that of scanning information generated by a vendor service that you simply can’t belief 100%.
Metadefender
Scanning information and internet pages on one endpoint will not be sufficient for some organizations. They’ve a posh info movement and not one of the endpoints could be compromised. For these use instances, Metadefender is the best resolution.
Consider Metadefender as a paranoid gatekeeper that sits between your most necessary information property and all the pieces else, together with the community. I say “paranoid” as a result of that is the design philosophy behind Metadefender. I can not describe this higher than them, so right here it goes:
Most cybersecurity options depend on detection as their essential protecting operate. MetaDefender’s information cleansing doesn’t depend on detection. It assumes that every one information could be contaminated and rebuilds the contents utilizing a secure and environment friendly course of. It helps greater than 30 file varieties and delivers secure and usable information. Information cleansing is extraordinarily efficient in stopping focused assaults, ransomware and different forms of identified and unknown malware threats.
There are some good options that Metadefender presents:
- Information Loss Prevention: Merely put, that is the flexibility to disregard and defend delicate info detected within the contents of information. For instance, a PDF receipt with the seen bank card quantity is made illegible by Metadefender.
- Deploy domestically or within the cloud (relying on how paranoid you might be!).
- Browse greater than 30 forms of archive codecs (zip, tar, rar, and so forth.) and 4,500 file sort spoofing tips.
- Multi-channel deployments: Safe information solely, or get began with electronic mail, community, and login auditing.
- Customized workflows to use several types of scan pipelines based mostly on customized guidelines.
Metadefender contains over 30 engines, however abstracts them properly so that you by no means have to consider them. If you happen to’re a medium to giant enterprise that may’t afford safety nightmares, Metadefender is a superb choice.
urlscan.io
If you happen to primarily cope with internet pages and have at all times wished a deeper perception into what they do behind the scenes, Urlscan.io is a wonderful weapon in your arsenal.

The quantity of knowledge that Urlscan.io throws away is nothing in need of spectacular. You will note, amongst different issues:
- A complete variety of IP addresses that the web page has contacted.
- Checklist of geographies and domains to which the web page has despatched info.
- Applied sciences used on the front-end and back-end of the location (no accuracy claims are made, however it’s alarmingly correct!).
- Area and SSL certificates info
- Detailed HTTP interactions together with request payload, server names, response instances and far more.
- Hidden redirects and failed requests
- Outgoing hyperlinks
- JavaScript evaluation (international variables used within the scripts, and so forth.)
- DOM tree evaluation, kind content material and extra.
That is the way it all seems to be:
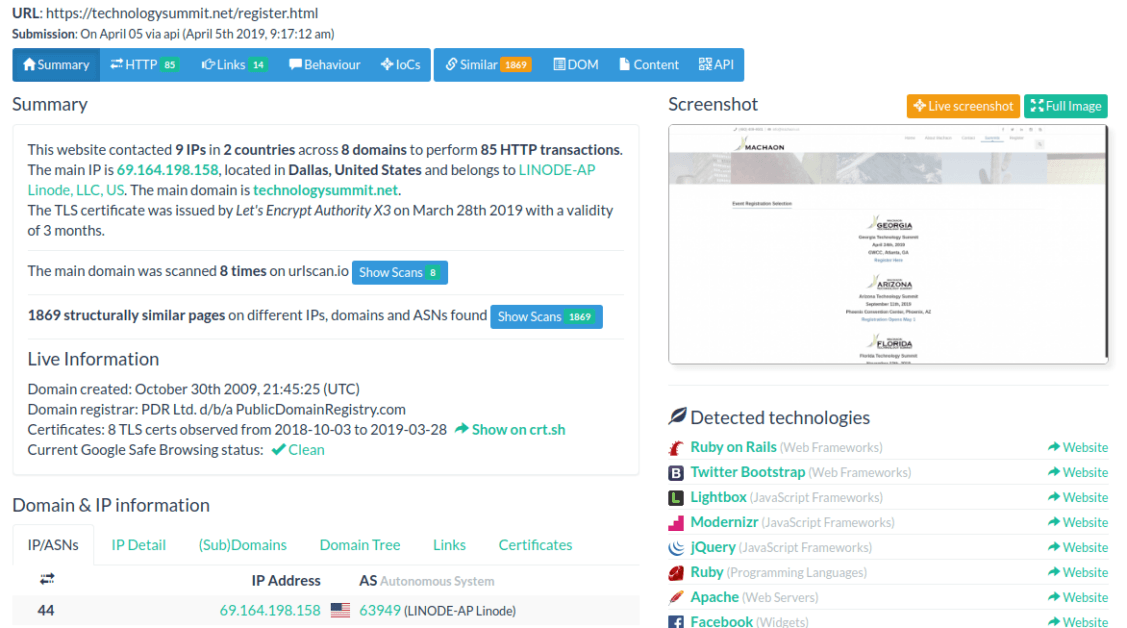
The API is straightforward and easy, permitting you to submit a URL to scan and verify that URL’s scan historical past (i.e. scans carried out by others). All in all, Urlscan.io presents a wealth of knowledge for any firm or particular person concerned.
JUICES
SUCURI is a well known platform relating to on-line scanning of internet sites for threats and malware. What you could not know is that additionally they have a REST API, permitting the identical energy to be leveraged programmatically.
There’s not a lot to speak about right here aside from the API is straightforward and works nicely. After all, Sucuri is not restricted to a scan API, so when you’re at it I might suggest trying out a few of its highly effective options, resembling server-side scanning (principally you present the FTP particulars, and it logs in and scans all information for threats!).
She is going to
Our final entry on this checklist is Quttera, which presents one thing somewhat totally different. As a substitute of scanning the area and submitted pages on demand, Quttera also can carry out steady monitoring so you possibly can keep away from zero-day vulnerabilities.
The REST API is straightforward and highly effective and may return a couple of extra codecs than JSON (e.g. XML and YAML). Full multithreading and concurrency are supported in scans, permitting you to run a number of deep scans in parallel. As a result of the service runs in real-time, it is invaluable to companies coping with mission-critical choices the place downtime is the doom.
Conclusion
Safety instruments like those lined on this article are simply an additional line of protection (or warning, if you’ll). Like an antivirus, these can do so much, however they can not present a flawless scanning technique by any means. That is just because a program written for malicious intent is similar to the pc as one written for optimistic impression: they each demand system assets and make community requests; the satan is within the context, which doesn’t enable computer systems to work efficiently.
That mentioned, these APIs present sturdy safety protection that’s fascinating most often – for exterior web sites in addition to your individual! 🙂

