VPNs are a factor of the previous. Zero-trust networks simply adapt to cloud, on-premises, or combined environments and supply larger flexibility and safety than VPNs. And decrease prices.
VPNs, or digital non-public networks, have been designed a number of a long time in the past to increase the attain of company knowledge networks past their bodily limits. The ubiquity of the Web and its low price of entry was the set off for corporations to start benefiting from it to attach branches, prospects, and suppliers in a single community, with out the necessity to use costly devoted connections.
The one massive difficulty that made implementation tough — and nonetheless does — was safety. Within the conventional network-centric work mannequin, safety dangers enhance exponentially as VPN-type accesses are added. An answer to this downside has now been discovered by way of non-network-centric alternate options to the standard VPN mannequin.
Historical past of VPNs

Connecting distant websites to an organization’s community through the Web all the time posed a major safety danger, as knowledge despatched from one web site to a different goes by way of public hyperlinks and may be seen by malicious eyes. That’s the reason VPNs have been created as tunnels by way of which info circulates in an encrypted method in order that it can’t be intercepted and utilized by strangers.
Customers with licensed entry to the VPN tunnel should have the means to encrypt and decrypt the data as transparently as potential, in a manner that doesn’t disturb or impede their widespread duties. Though the VPN creates a digital and encrypted channel between customers and a corporation’s community, its downside is that any breach that happens in that channel offers potential attackers limitless entry to all assets linked to the group community, which creates a danger of nice proportions.
As well as, organizations with giant numbers of distant customers — for instance, staff, prospects, or suppliers — should handle entry by way of the VPN for every of them, which suggests excessive upkeep prices. The state of affairs turns into much more difficult when comparatively new units, resembling cell or IoT, have to be introduced into the community. At that time is when the VPN stops being an answer and begins to turn out to be a significant issue.
Zero belief networks

In a zero-trust community mannequin, the fundamental precept is that nobody is trusted.
Entry of all customers to community assets is restricted, no matter whether or not they have accessed the identical useful resource earlier than or not. Any person or system trying to entry a useful resource inside a zero-trust community should undergo a strict — albeit quick — verification and authentication course of, even when the person or system is bodily inside the group.
The zero belief mannequin can add some complexity to your implementation. Permits and authorizations have to be stored up-to-date and precisely outlined. It requires a bit extra work in that sense, however what you get in return is bigger management over entry to assets and a discount within the surfaces weak to assault.
As well as, different advantages of recent alternate options to VPNs — resembling zero-trust networks — embrace a greater person expertise for distant customers, which is evidenced by greater high quality video conferencing and extra responsive functions. On the similar time, managing entry by particular assets reduces the chance of lateral actions, and consequently, the potential unfold of ransomware.
No requirements in the intervening time
Whereas there are a number of initiatives to outline protocols, procedures, and applied sciences for zero belief architectures, there are not any industry-wide accepted requirements but. Nonetheless, a number of zero-trust community options are rising as leaders on this new section, so they might nicely be those that find yourself setting the requirements.
Let’s have a look 👀 at them.
NordLayer
NordLayer supplies a full service for conserving the community safe and ensures safe distant entry to what you are promoting knowledge. It leverages modern applied sciences inside the Safe Service Edge framework derived from the Safe Entry Service Edge mannequin.
Going past the traditional cybersecurity means, NordLayer helps a perimeter-less office. NordLayer helps many endpoint varieties, together with Home windows, macOS, Linux, Android, and iOS working techniques. As soon as NordLayer’s functions are put in, these units can be utilized to entry the inner firm’s community.
Their service supply methodology is straightforward sufficient for informal customers to arrange on their units whereas offering in-depth performance for community directors. That manner, customers get a easy service they’ll depart operating within the background, whereas community directors can benefit from in-depth cybersecurity controls.
Safe Net Gateways management the inner entry as checkpoints for every incoming connection’s analysis. The system’s safety posture is checked with jailbroken system detection, removing suspicious units that might threaten the community’s safety standing.
As for person administration, NordLayer emphasizes identity-based authentication. Your workforce may be positioned in particular groups with adjustable entry ranges. Such worker segmentation will increase community visibility by guaranteeing that staff are solely accessing assets obligatory for his or her work capabilities.
Authentication itself may be enhanced by two-factor authentication utilizing biometric knowledge, a TOTP app, or SMS authentication. That manner, the hackers would nonetheless simply infiltrate your community even when your worker’s credentials are uncovered.
Whereas NordLayer began from a enterprise VPN service, they’ve since expanded their suite, providing a complete resolution that’s far superior by way of safety and options.
Twingate
Supplied as a cloud-based service, Twingate makes it potential for IT groups to configure a software-defined perimeter for his or her assets with out the necessity to make any infrastructure modifications, and centrally handle person entry to inside functions, both on-premises or in cloud environments.
Twingate considerably reduces the group’s publicity to cyber-attacks, making the inner community fully invisible to the Web. Useful resource-level entry management prevents hackers from having access to the whole community, even once they handle to compromise particular person customers or assets.
Twingate resolution requires minimal upkeep and is able to scaling from 10 to 10,000 assets. Entry administration to assets is carried out from a central web-based administration console, referred to as the Twingate controller. To authenticate customers and be sure that every useful resource requirement comes from a certified person, Twingate integrates with main SSO (single sign-on) and id suppliers.
A particular characteristic of Twingate is Break up Tunneling, which permits site visitors to circulate by way of the group’s community solely when obligatory. This reduces latency in functions resembling videoconferencing, the place events may be extra instantly linked.
The Twingate service is charged at a per-user, per-month, which varies relying on the variety of customers. A free choice is obtainable that helps as much as 2 customers, two units per person, and one distant community.
Perimeter 81
Perimeter 81 means that you can create, handle simply, and safe customized and multi-regional networks that interconnect to a corporation’s on-premises or cloud environments. Perimeter 81’s Zero Belief Safe Community as a Service employs a software-defined perimeter structure, which supplies larger community visibility, flexibility for onboarding new customers, and compatibility with main cloud infrastructure suppliers.
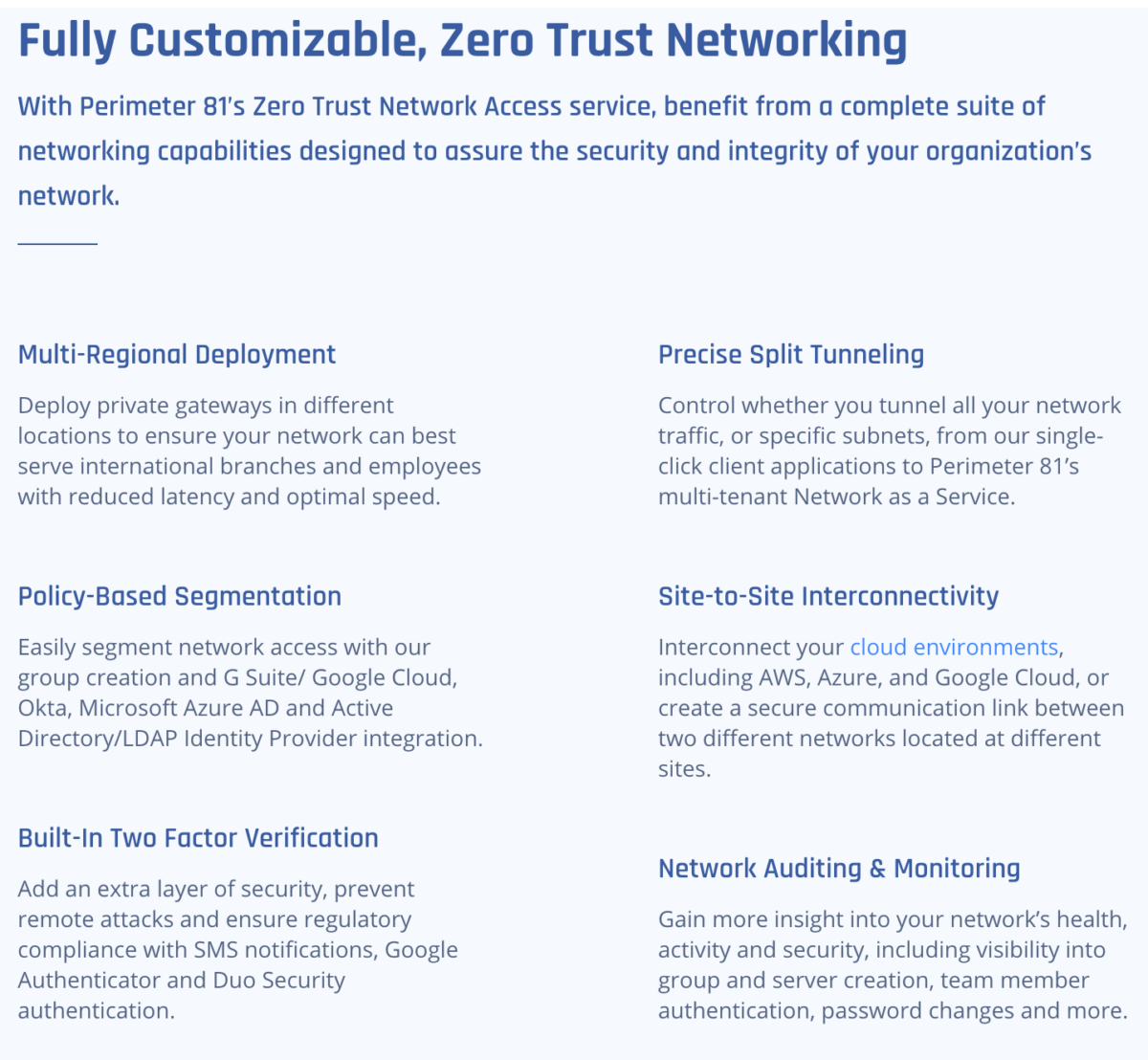
A community segmentation outlined by trusted zones permits the group to create inside belief boundaries that management the circulate of information site visitors in a granular manner. Trusted zones are made up of units of infrastructure components during which assets function on the similar degree of belief and supply related performance, minimizing the variety of communication paths and constantly limiting threats.
With Perimeter 81’s Zero Belief Community Entry, it’s potential to have an entire and centralized view of the group’s community, guaranteeing least-privilege entry to all priceless company assets. Its security measures adhere to the SASE mannequin, a time period coined by Gartner that refers back to the convergence of safety and community administration on the identical platform.
Cloudflare for Groups
Constructed by itself world infrastructure, Cloudflare for Groups service supplies safe entry to a corporation’s units, networks, and functions, changing conventional network-centric safety perimeters and making the Web quicker and safer for work groups distributed everywhere in the world.
Cloudflare provides zero-trust entry to all functions within the group, authenticating customers by way of its personal world community. On this manner, it permits the incorporation of third-party customers effortlessly and conserving a document log for every occasion and for every entry request to a useful resource.
The Cloudflare for Groups resolution is constructed round two complementary merchandise: Cloudflare Entry and Cloudflare Gateway.
The primary fulfills a operate analogous to that of a VPN: giving customers entry to the assets they want, avoiding exposing them to cyber threats. And the second is a firewall that protects customers from malware infections, sustaining group insurance policies each time they hook up with the Web.
Each Entry and Gateway are constructed on prime of the Cloudflare community. Meaning they’re able to delivering excessive pace, reliability, and scalability to even the biggest organizations. The community is proof against DDoS assaults and is milliseconds away from wherever customers are.
Cloudflare for Groups plans is split into Free, Normal, and Enterprise.
The Free model provides the important instruments to guard as much as 50 customers and functions. If the variety of customers is bigger than 50, it’s essential to improve to the Normal model for a charge of $ 7 per person and per thirty days, and if enterprise capabilities are required, resembling 24x7x365 telephone and chat assist, certificate-based authentication, and many others., you want to scale to the Enterprise model, for a price tailor-made to every case.
Zscaler Non-public Entry
Safety-as-a-service firm Zscaler provides a cloud-based zero-trust networking service — referred to as Zscaler Non-public Entry, or ZPA — that controls entry to personal functions, whether or not they run in public clouds or inside a proprietary knowledge middle. ZPA ensures that functions are by no means uncovered to the Web, making them fully invisible to unauthorized customers.
The ZPA service connects functions with customers by way of an inside-out strategy, slightly than by stretching the boundaries of the community to incorporate customers. Customers are by no means inside the community, minimizing the dangers of lateral motion or the unfold of ransomware. This zero-trust community entry technique helps each managed and unmanaged units and likewise helps any sort of non-public utility, not simply net functions.
Via the institution of micro tunnels, ZPA offers community directors the flexibility to section by utility, with out the necessity to use classical community segmentation or to section artificially by managing entry ranges or firewall insurance policies. Using tunnels with TLS encryption and customized non-public keys (PKI) supplies an additional degree of safety for accessing company functions.
At a time when distant work appears to be right here to remain, Zscaler is emphasizing supporting customers to allow them to work from anyplace with out shedding productiveness.
TeamViewer
TeamViewer resolution proposes distant entry to units as a substitute for VPNs, providing benefits by way of pace, safety, performance, and price. TeamViewer is the most well-liked distant entry resolution, with greater than 2 billion linked units and 200 million energetic customers.
Connecting to a distant system through TeamViewer maximizes connection pace by sending solely the data required to supply interactivity over the community, which reduces the amount of knowledge transmitted. In flip, info safety is ensured by end-to-end knowledge encryption, coupled with extra safety measures, resembling two-factor authentication.
With TeamViewer, distant units may be shared amongst a number of customers concurrently. Apart from, the answer provides further performance, resembling file or display screen sharing and session recording.
The prices of organising and sustaining a VPN are estimated to be a number of instances greater than these of distant entry options, that are freed from difficult set up and configuration procedures. For individuals who are taken with utilizing TeamViewer privately, there’s a free model with which you’ll give pals or household distant entry to your pc or system. This resolution consists of the potential for sharing recordsdata and screens and sustaining communication by audio, video, or chat.
Taking good care of the well being of sysadmins
Zero belief options are, at first, a treatment for a lot of complications that sysadmins undergo from VPNs. Any enterprise proprietor who desires to scale back medical bills and stress therapies for his or her IT division ought to critically take into account adopting an excellent various to the just about outdated VPNs, resembling the fashionable zero-trust networks and distant entry choices reviewed right here.

